Alerts
Zeus targeted attacks continue
Date:02.11.2010
Threat Type: Malicious Web Site / Malicious Code
Websense Security Labs™ ThreatSeeker™ Network has discovered a follow up attack on Zeus campaign targeting government departments. Its research shows that once again the campaign is targeting workers from government and military departments globally.
Figure 1 - Zeus Campaign: 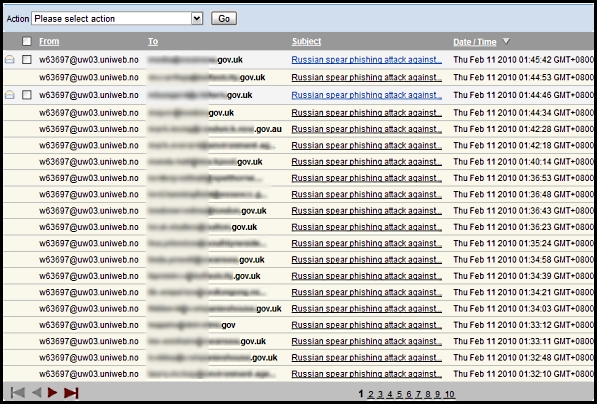
The Websense ThreatSeeker Network has seen thousands of emails pretending to be from a reputable figure within the Central Intelligence Agency (see Figure 2). The email subject is: "Russian spear phishing attack against .mil and .gov employees"
Figure 2 - Content of the email: 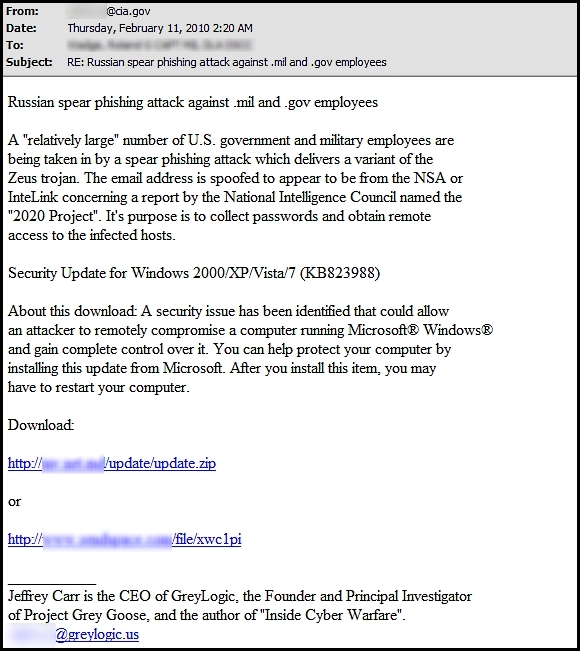
Jeffery Carr, the spoofed victim himself, has published a comment regarding this attack: 
The spoofed emails capitalize on the last Zeus attack, and claim that installing the Windows update via the links provided will aid protection against Zeus attacks. The binary file downloaded from these links is identified as a Zeus bot and holds 35% AV detection rate. Once again URLs in the email messages lead to a malicious file hosted on a compromised host, and also on a popular file hosting service. Once installed, the bot has identical functionality to the one mentioned in the previous alert. After The Zeus Rootkit component is installed the C&C server at update[removed].com is contacted to download an encrypted configuration file. Another data stealing component gets downloaded and installed from the same C&C in the shape of a Win32 Perl script compiled with Perl2Exe - this data-stealing component has only a 5% AV detection rate. Then the bot starts to connect with a credential-based FTP server at pack[removed].com to upload stolen data. The Zeus bot is normally designed to steal banking credentials; however it has also been seen in targeted attacks to steal other sensitive data.
Websense® Messaging and Websense Web Security customers are protected against this attack.


























