Alerts
Zeus Campaign Targeted Government Departments
Date:02.08.2010
Threat Type: Malicious Web Site / Malicious Code
Websense Security Labs™ ThreatSeeker™ Network has discovered a new Zeus campaign (a banking data stealing Trojan) which is now targeting government departments. Our research shows that the campaign has especially targeted workers from government and military departments in the UK and US: we found most victims' email addresses end with .gov.
Figure 1 - Zeus Campaign: 
Our ThreatSeeker™ Network has seen thousands of emails which pretend to be from the National Intelligence Council (see Figure 2). The email subjects include: "National Intelligence Council"
"RE: National Intelligence Council"
"Report of the National Intelligence Council"
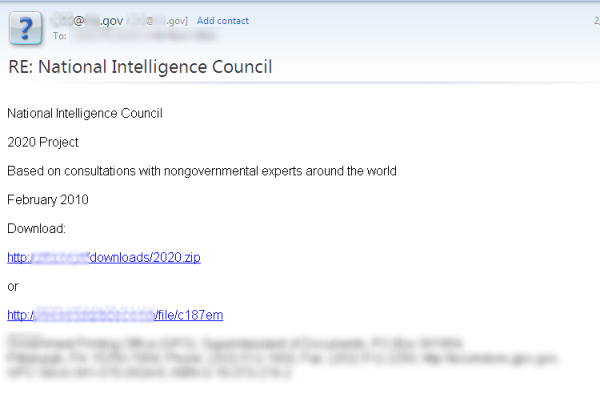
The spoofed emails lure victims to download a document about the "2020 project"; this is actually a Zeus bot. The Web sites which host the bot look very trustworthy: one of them is a compromised organization Web site and the other is located on a popular file hosting service. The bot has rootkit capabilities and connects to C&C servers at update[removed].com and pack[removed].com to report back on a successful infection and to download some archives with DLLs, it also modifies the hosts file to prevent updates from popular anti-virus vendors.
Websense® Messaging and Websense Web Security customers are protected against this attack, however the anti-virus detection rate for this bot is currently at 26/40.


























